Understand SBOM and how Docker SBOM generates a list of software of the container images to prevent any threat.
The Log4j vulnerability and SolarWinds supply chain attack have made us realize that software supply chains are at great risk of being targeted by attackers. The Docker SBOM helps detect these risks.
Software supply chain security comprises everything required to build, deliver and run software anywhere with confidence. It ensures that not only software but the infrastructure, operating systems, source code repositories, registries, developers who wrote it, and the cloud services it uses don’t pose any threats.
The Software Bill of Materials (SBOM) has emerged as the first step to ensure software security.

What is SBOM and how does it help businesses?
An SBOM(Software Bill of Materials) is a list of software components that build the software product. It details the software package, content, license, and certificate information, just like packaged food items contain ingredients and other information.
SBOMs help organizations know and keep track of all software components along with other details, such as:
- Determining all the runtime dependencies of the software.
- Keeping track of critical updates and patches.
- Reducing supply chain attacks and ensuring the organization doesn’t use vulnerable components.
- Detecting license and certificate-related issues.
The National Telecommunications and Information Administration (NTIA) has listed the minimum requirements for the SBOM, which are:
- Software supplier and author of SBOM.
- Information about software vendors.
- Software component name and its version.
- Unique identifier for each component.
- Relationship of the component with other components and packages.
- Timestamp of SBOM creation.
SBOM standards
To make organizations adopt SBOM quickly, several standards have been defined for generating them. A defined schema provides a format for listing software components, and the most widely used are Software Package Data Exchange (SPDX) and CycloneDX.
SPDX
SPDX is an SBOM format developed by the Linux Foundation. It shows relationships between software components, licenses, and copyrights associated with the software. It can be stored in different file formats, such as SPDX and JSON. It defines three elements: documents (metadata about the SBOM), packages (groups of elements), and files (single files).
CycloneDX
This lightweight SBOM standard is maintained by the OWASP community and built on top of SPDX. It gives security-related information such as supplier, manufacturer, target components, etc. It can be stored in different file formats, such as XML and JSON. It gets divided into components, services, and dependencies.
Docker, too, has recently introduced an SBOM format for container images. It has announced the docker sbom CLI command in Docker Desktop 4.7.0 as a CLI plugin, which lists all the components of the container image. It is an experimental functionality for now, which has been developed as an open-source collaboration with Anchore through the Syft tool.
Syft is a tool for generating SBOMs from container images and file systems. It can convert SBOMs to different formats.
Installation of the Docker CLI plugin
- As a pre-requisite, Docker/Docker Desktop must be installed on your system. Upgrade the Docker desktop if its version is less than 4.7.0.
apt update && apt install docker.io -y
Note: If you are using Docker as a CLI tool, then before installing docker sbom create a /root/.docker directory. More information can be found at https://github.com/docker/sbom-cli-plugin/issues/25
mkdir -p /root/.docker/cli-plugins
- Install the docker sbom plugin.
curl -sSfL https://raw.githubusercontent.com/docker/sbom-cli-plugin/main/install.sh | sh -s --
- Check its version and verify installation:
docker sbom version
Different Docker SBOM commands
- To check all options related to docker sbom
docker sbom --help
- To list the software components of an
NGINXDocker image
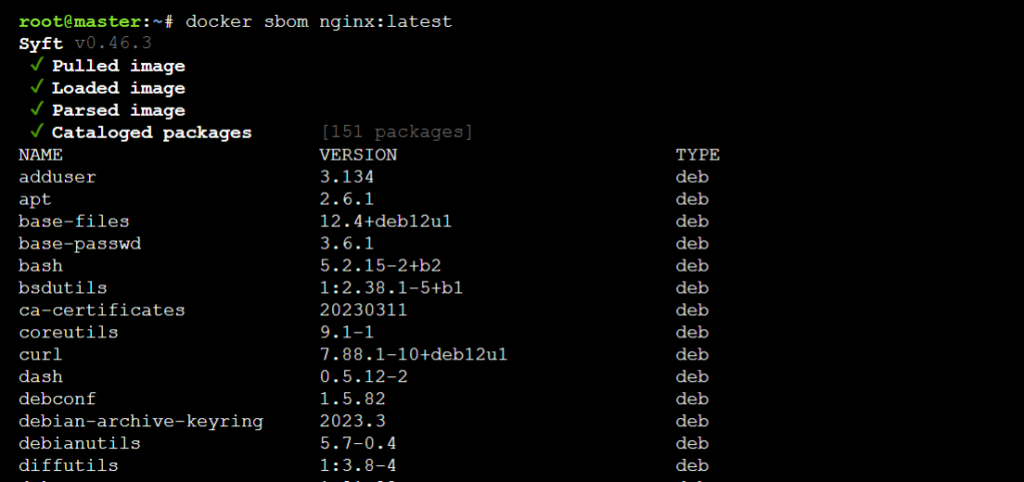
docker sbom nginx:latest
By default, the output will be in a table format. From the output given below, it can be inferred that the first image is pulled if not present locally, then it’s loaded and processed further, and then the software elements get listed along with its version and package type.
- To list the software components of a particular Node.js application, type:
docker sbom oshi36/nodeapp_test:latest
One will get the similar output as shown below
docker sbom oshi36/nodeapp_test:latest Syft v0.46.3 ✔ Pulled image ✔ Loaded image ✔ Parsed image ✔ Cataloged packages [569 packages] NAME VERSION TYPE JSONStream 1.3.5 npm abbrev 1.1.1 npm accepts 1.3.8 npm agent-base 4.2.1 npm agent-base 4.3.0 npm agentkeepalive 3.5.2 npm ajv 5.5.2 npm alpine-baselayout 3.2.0-r3 apk alpine-keys 2.1-r2 apk ansi-align 2.0.0 npm ansi-regex 2.1.1 npm ansi-regex 3.0.0 npm ansi-styles 3.2.1 npm ansicolors 0.3.2 npm ansistyles 0.1.3 npm apk-tools 2.10.5-r0 apk aproba 1.2.0 npm aproba 2.0.0 npm archy 1.0.0 npm are-we-there-yet 1.1.4 npm array-flatten 1.1.1 npm asap 2.0.6 npm asn1 0.2.4 npm assert-plus 1.0.0 npm asynckit 0.4.0 npm aws-sign2 0.7.0 npm aws4 1.8.0 npm balanced-match 1.0.0 npm bcrypt-pbkdf 1.0.2 npm bin-links 1.1.7 npm bluebird 3.5.5 npm body-parser 1.20.1 npm boxen 1.3.0 npm
- To write the SBOM report to a file, use the output flag:
docker sbom oshi36/nodeapp_test:latest --output nodeapp_report
Open the output file nodeapp_report
cat nodeapp_report
- To skip paths from docker sbom to scan, use the exclude flag
docker sbom oshi36/nodeapp_test:latest --exclude /usr/local
From the output given below, it can be seen that docker sbom leaves the elements to be scanned at the /usr/local location.
- To get the SBOM of platform-specific container images such as linux/arm64, arm64, etc, use the platform flag:
docker sbom nginx:alpine --platform linux/arm64
- To get the SBOM report in different SBOM formats such as
spdx-json,cyclonedx-json,syft-json, etc, use theformatflag:
docker sbom oshi36/nodeapp_test:latest --format spdx-json
In this format, a unique identifier SPDXID is provided for each package and file, along with information about the license. One will get similar output as shown below.
{
"SPDXID": "SPDXRef-DOCUMENT",
"name": "oshi36/nodeapp_test-latest",
"spdxVersion": "SPDX-2.2",
"creationInfo": {
"created": "2023-08-14T08:55:44.992806046Z",
"creators": [
"Organization: Anchore, Inc",
"Tool: syft-v0.46.3"
],
"licenseListVersion": "3.17"
},
"dataLicense": "CC0-1.0",
"documentNamespace": "https://anchore.com/syft/image/oshi36/nodeapp_test-latest-b4b926ff-67ea-4a90-b9ca-77375b5d4d62",
"packages": [
{
"SPDXID": "SPDXRef-2a0a99c2a38a6407",
"name": "JSONStream",
"licenseConcluded": "NOASSERTION",
"downloadLocation": "git://github.com/dominictarr/JSONStream.git",
"externalRefs": [
{
"referenceCategory": "SECURITY",
"referenceLocator": "cpe:2.3:a:JSONStream:JSONStream:1.3.5:*:*:*:*:*:*:*",
"referenceType": "cpe23Type"
},
{
"referenceCategory": "SECURITY",
"referenceLocator": "cpe:2.3:a:*:JSONStream:1.3.5:*:*:*:*:*:*:*",
"referenceType": "cpe23Type"
},
{
"referenceCategory": "PACKAGE_MANAGER",
"referenceLocator": "pkg:npm/JSONStream@1.3.5",
"referenceType": "purl"
}
],
"filesAnalyzed": false,
"homepage": "http://github.com/dominictarr/JSONStream",
"licenseDeclared": "NOASSERTION",
"originator": "Person: Dominic Tarr <dominic.tarr@gmail.com> (http://bit.ly/dominictarr)",
"sourceInfo": "acquired package info from installed node module manifest file: /usr/local/lib/node_modules/npm/node_modules/JSONStream/package.json",
"versionInfo": "1.3.5"
},
.....docker sbom oshi36/nodeapp_test:latest --format cyclonedx-json
This format has details about the supplier, manufacturer, and BOM creation tools, along with the component type and its version in the hash. One will get similar output as shown below.
{
"bomFormat": "CycloneDX",
"specVersion": "1.4",
"serialNumber": "urn:uuid:485ca879-9cf8-4dd0-a3ba-30837b144e43",
"version": 1,
"metadata": {
"timestamp": "2023-08-14T08:58:11Z",
"tools": [
{
"vendor": "anchore",
"name": "syft",
"version": "v0.46.3"
}
],
"component": {
"bom-ref": "ca3081e98a696b2a",
"type": "container",
"name": "oshi36/nodeapp_test:latest",
"version": "sha256:f5b479b7050956bdfcea3f1af9000a85dc0dd358ee674a2b29ebfb0ed3a846bd"
}
},
"components": [
{
"bom-ref": "pkg:npm/JSONStream@1.3.5?package-id=2a0a99c2a38a6407",
"type": "library",
"author": "Dominic Tarr \u003cdominic.tarr@gmail.com\u003e (http://bit.ly/dominictarr)",
"name": "JSONStream",
"version": "1.3.5",
"cpe": "cpe:2.3:a:JSONStream:JSONStream:1.3.5:*:*:*:*:*:*:*",
"purl": "pkg:npm/JSONStream@1.3.5",
"externalReferences": [
{
"url": "git://github.com/dominictarr/JSONStream.git",
"type": "distribution"
},
{
"url": "http://github.com/dominictarr/JSONStream",
"type": "website"
}
],
.....docker sbom oshi36/nodeapp_test:latest --format syft-json
It outputs the SBOM report in Syft’s native JSON format. One will get similar output as shown below.
{
"artifacts": [
{
"id": "2a0a99c2a38a6407",
"name": "JSONStream",
"version": "1.3.5",
"type": "npm",
"foundBy": "javascript-package-cataloger",
"locations": [
{
"path": "/usr/local/lib/node_modules/npm/node_modules/JSONStream/package.json",
"layerID": "sha256:8ca4f4055a7095ff1807ce521287ae7bdd91aa711ae45d5b0f3d1c45ab0adefe"
}
],
"licenses": [
"(MIT OR Apache-2.0)"
],
"language": "javascript",
"cpes": [
"cpe:2.3:a:JSONStream:JSONStream:1.3.5:*:*:*:*:*:*:*",
"cpe:2.3:a:*:JSONStream:1.3.5:*:*:*:*:*:*:*"
],
"purl": "pkg:npm/JSONStream@1.3.5",
"metadataType": "NpmPackageJsonMetadata",
"metadata": {
"name": "JSONStream",
"version": "1.3.5",
"author": "Dominic Tarr <dominic.tarr@gmail.com> (http://bit.ly/dominictarr)",
"licenses": [
"(MIT OR Apache-2.0)"
],
"homepage": "http://github.com/dominictarr/JSONStream",
"description": "",
"url": "git://github.com/dominictarr/JSONStream.git"
}
},
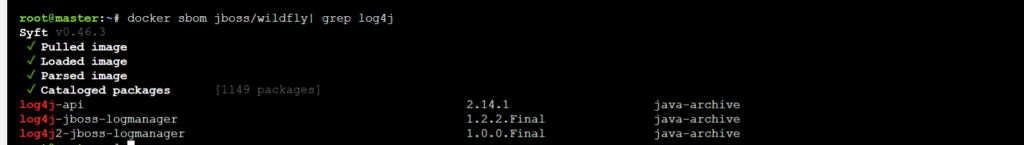
....Log4j 2 vulnerability use case
Log4j 2 is a logging library by Apache and its vulnerability CVE-2021-44228 allows remote code execution from a context that is easily available to an attacker. This vulnerability has been found in Minecraft servers. It allows commands to be typed in chat logs and then sent to the logger.
Currently, CVE-2021-44228 impacts all versions of Log4j 2.x <= 2.14.1. If the container image has Log4j, then docker sbom can help in finding out its version and deciding whether it’s vulnerable or not.
- To list the components of jboss/wildfly application server and find whether its Log4j version is vulnerable or not.
docker sbom jboss/wildfly| grep log4j
From the output given below it can be seen clearly that Log4j is vulnerable to CVE-2021-44228 due to its version.
Conclusion
To sum up, docker sbom helps in generating the SBOM for the container image, which helps identify and solve any dependency issues.

